Blog
Evaluating Card Access Control Systems for Enhanced Security Efficiency and Cost Effectiveness
In the ever-evolving landscape of security management, the importance of efficient access control cannot be overstated. According to a recent report by MarketsandMarkets, the global market for Card Access Control Systems is projected to reach $9.9 billion by 2025, representing a significant growth driven by the increasing need for enhanced security measures in various sectors.
As organizations seek to fortify their physical security frameworks, evaluating the effectiveness and cost-efficiency of these systems becomes paramount. In light of rising security threats and evolving technological advancements, a comprehensive analysis of Card Access Control Systems not only highlights their role in preventing unauthorized access but also reveals how they can optimize operational costs while ensuring robust security protocols. This tutorial aims to provide insights into the critical factors to consider when assessing these systems, helping stakeholders make informed decisions that align with their security objectives.
Understanding the Importance of Card Access Control Systems in Modern Security Strategies
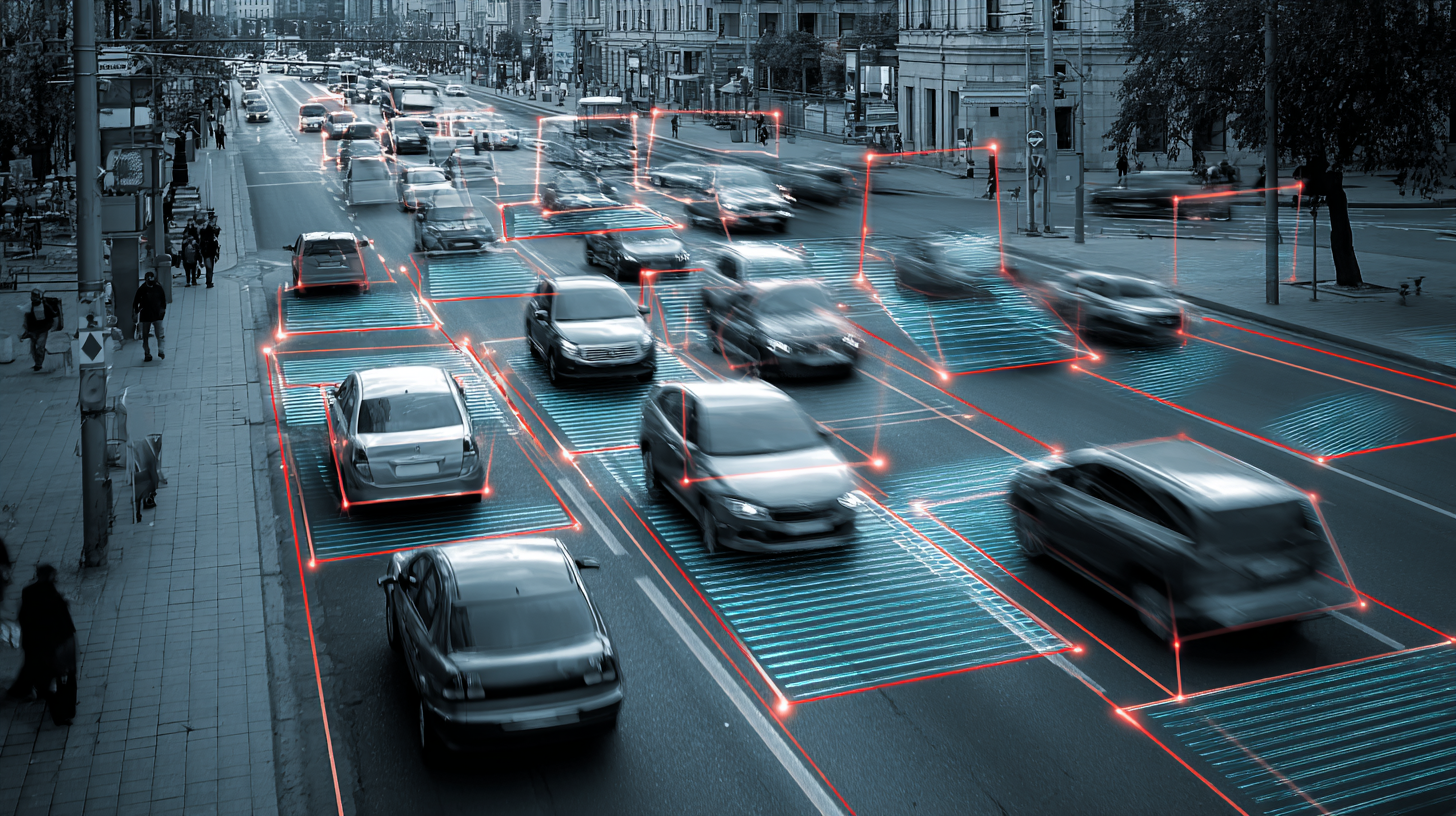
In today’s rapidly evolving security landscape, card access control systems have become crucial components of modern security strategies. These systems not only streamline access management within various facilities but also enhance overall security by ensuring that only authorized personnel can enter sensitive areas. By integrating technology with physical security, organizations can monitor access points in real-time, providing a comprehensive view of who is entering and exiting facilities. This level of control is essential in preventing unauthorized access and protecting valuable assets.
Moreover, the importance of card access control systems extends beyond mere security measures. These systems contribute to operational efficiency by simplifying the process of managing access permissions. Organizations can easily update or revoke access for employees, visitors, or contractors, reducing the logistical challenges associated with traditional key systems. Additionally, many modern systems are designed to be cost-effective, offering scalable solutions that cater to businesses of all sizes. As organizations increasingly recognize the benefits of integrating robust security measures, card access control systems stand out as a foundational element in safeguarding their environments.
Evaluating Card Access Control Systems for Enhanced Security Efficiency and Cost Effectiveness
| System Type | Security Features | Cost Effectiveness (Annual) | User Management | Integration Capabilities |
|---|---|---|---|---|
| Proximity Card System | Basic Encryption, Lost Card Deactivation | $1,000 - $2,000 | Up to 500 Users | Limited API Integration |
| Smart Card System | Advanced Encryption, PIN Authentication | $2,500 - $4,000 | Up to 1,000 Users | Robust API and Third-Party Integration |
| Biometric Access System | Fingerprint, Facial Recognition, Anti-Spoofing | $5,000 - $10,000 | Up to 5,000 Users | High Compatibility with Various Systems |
| Mobile Access System | Mobile Credentialing, Remote Access | $3,000 - $6,000 | Unlimited Users | Seamless Integration with Smart Devices |
Key Metrics for Assessing the Effectiveness of Card Access Control Systems in Various Industries
The growing integration of emerging technologies in door lock systems is revolutionizing security measures across various industries. As organizations strive to enhance security efficiency and reduce costs, the adoption of advanced card access control systems has gained significant traction. One pivotal metric for evaluating these systems is the speed and accuracy of authentication. Features such as biometric authentication methods, including fingerprint and facial recognition, are becoming increasingly prevalent. These technologies not only streamline the access process but also mitigate the risks associated with lost or stolen access cards.
Moreover, the scalability of card access control systems is crucial for organizations looking to adapt to changing security needs. Businesses can assess system effectiveness by examining factors such as user management, system integration capabilities, and real-time monitoring. As the demand for layered security increases, increasingly sophisticated access control systems that leverage emerging technologies will be essential. This ensures not only enhanced safety for personnel and assets but also greater efficiency in operational management, making it a strategic investment for the future.

Cost-Benefit Analysis: Balancing Security Investment and Operational Efficiency
The cost-benefit analysis (CBA) has become a critical framework in evaluating various investments, particularly in security systems like card access control. Recent studies reveal that companies implementing unified cybersecurity platforms have seen significant reductions in operational costs, with estimates suggesting savings of up to 30% in overall security expenditures. Such platforms not only enhance visibility and strengthen defenses but also streamline operations, further improving efficiency. This mirrors findings from reviews of sustainable upgrades in existing buildings, where a strategic approach to CBA has led to an average ROI increase of 20% through energy-saving solutions and infrastructure improvements.
Moreover, as artificial intelligence continues to reshape industries, its integration within access control systems could provide an additional cost-effective layer of security. Industry reports forecast that by 2025, AI is expected to drive efficiency gains of up to 40% in operational processes, enabling organizations to allocate resources more effectively. As businesses aim to balance security investments with operational efficiency, leveraging advanced technologies while conducting thorough CBA can yield significant financial and security benefits in a competitive landscape.
Cost-Benefit Analysis of Card Access Control Systems
This chart illustrates a comparative analysis of the investment costs versus the operational efficiency gains from implementing card access control systems across various sectors.
Emerging Technologies in Card Access Control: Trends Shaping the Future of Security
As the security landscape evolves, the integration of emerging technologies in card access control systems is driving significant market growth and enhancing security efficiency. Biometric authentication methods, such as fingerprint and facial recognition, are becoming standard components of modern access control solutions. These technologies not only improve security by minimizing the risks associated with lost or stolen cards but also streamline the user experience, allowing for a quicker and more convenient entry process.
Furthermore, advancements in artificial intelligence and machine learning are reshaping the way access control systems respond to threats. By leveraging data analytics, these systems can identify unusual patterns or behaviors, triggering alerts for unauthorized access or potential security breaches in real time. As organizations increasingly prioritize robust security measures in their facilities, the adoption of these innovative technologies is likely to become widespread, ensuring a more resilient and adaptive approach to security management.

Best Practices for Implementing and Maintaining Card Access Control Systems for Optimal Performance
Implementing card access control systems requires careful attention to best practices to ensure optimal performance. First and foremost, organizations should assess their security needs and choose a system that can scale with their growth. This involves selecting the right hardware and software that can handle the desired number of users and entry points while providing reliable authentication methods such as biometric options or two-factor authentication for added security.
Once the system is in place, regular maintenance is crucial. This includes updating software to protect against vulnerabilities, conducting routine audits to ensure compliance, and training employees on the proper use of the system. Additionally, a comprehensive access management policy should be established to regulate user privileges and monitor access logs for any suspicious activity.
By following these best practices, organizations can enhance the efficiency and cost-effectiveness of their card access control systems while ensuring robust security measures.
Related Posts
-

Global Reach of China's Leading Door Access Control Systems: Setting the Standard Worldwide
-

Navigating Challenges in Choosing the Right Card Access Control Systems for Your Business
-

How to Choose the Right Access Control System for Your Global Business Needs
-

Understanding Global Industry Standards for the Best Biometric Access Control Solutions
-

Future Innovations in Best Door Access Control Technology for 2025
-

Mastering Industry Compliance for the Best CCTV Camera Installation Guide
